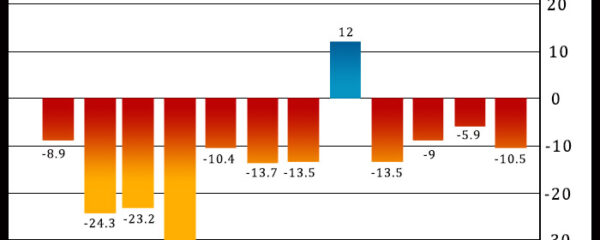
Philadelphia-area manufacturing activity unexpectedly contracted at an accelerated rate in the month of December, according to a report released by the Federal Reserve Bank of […]
wcoinnews.com
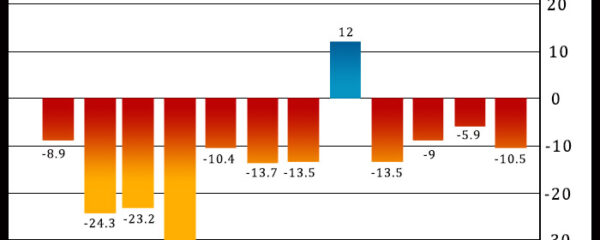
Philadelphia-area manufacturing activity unexpectedly contracted at an accelerated rate in the month of December, according to a report released by the Federal Reserve Bank of […]



EXCLUSIVESuspended Tube driver who sparked fury by leading chant of ‘free free Palestine’ on Underground train is interviewed by police Video from October showed ‘Free […]



As we enter 2024, the crypto realm stands poised at a crucial juncture marked by projections, debates, and, most importantly, the prospect of a Bitcoin […]

Biotechnology company Biogen Inc. (BIIB) Friday announced its agreement to acquire Reata Pharmaceuticals, Inc. (RETA) for $172.50 per share in cash, reflecting an enterprise value […]



UK consumer price inflation reached its lowest level in more than two years in November, strengthening calls for early rate cuts even as Bank of […]



Cryptocurrencies gained more than 3 percent in the past 24 hours amidst lingering excitement about a likely regulatory approval for a spot Bitcoin ETF product. […]



A popular cryptocurrency analyst has recently suggested that the meme-inspired cryptocurrency Dogecoin could see a “gorgeous pump” over the holidays after it breaks through a […]

